Penetration Testing Services
No generic processes. No false positives. Just clear, credible results from experts who guide you every step of the way. Get a tailored cyber security assessment and direct support, so you’re always confident in your security.




Get a fast pen test quote:
Why choose CodeShield penetration testing Services?
End-to-end
service
Work with a dedicated expert from start to finish. No handoffs, no confusion. Seamless coordination, with the same specialist guiding your cyber security assessment, testing, and results.
Transparent,
Fair Pricing
Our precise, tailored approach means you only pay for what matters. Targeted, efficient security penetration testing delivers the best value for your investment.
Professional
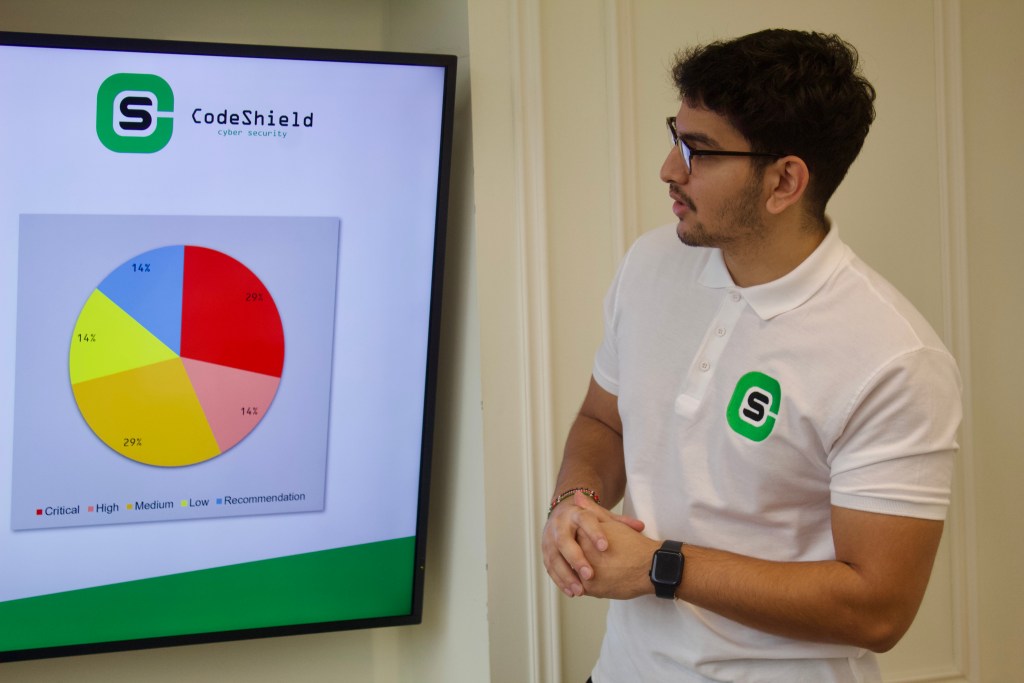
Reporting
Get reports that cut through the noise. Understand your real risks with straightforward, practical advice, so you know exactly what to fix and why.
Continuous
Support
Our commitment doesn’t end with the report. Ongoing guidance helps you close gaps and stay resilient as threats evolve. CodeShield is a penetration testing company you can rely on.
Real Experts. Real Testing.
Real Security.
Stay ahead of cyber threats with expert-led, controlled penetration testing services, no generic checklists, no guesswork. CodeShield’s specialists go beyond standard approaches, tailoring every engagement to your exact needs, whether it’s web app, network, mobile, cloud or social engineering.
Work directly with your assigned expert to define a truly bespoke project that delivers real value, not just a compliance checkbox. Our penetration testing builds confidence with clients and stakeholders, while helping you meet standards like ISO, PCI DSS, SOC 2 and more.

Benefits of penetration testing services
Curious whether penetration testing is worth the investment? Here’s how your organisation can benefit:
Uncover real-world security weaknesses across your networks, systems, and applications before attackers do.
Go beyond automated scans with expert-led, risk-prioritised findings that highlight what matters most.
Receive clear, actionable insights that support both immediate fixes and long-term resilience.
Demonstrate due diligence to clients, stakeholders, and regulators with verified security testing.
Meet compliance requirements with ISO 27001, GDPR, PCI DSS, with expert-led web application security testing.
Is penetration testing right for your organisation?
If you operate digital systems or store sensitive data, ask yourself:
Could an attacker exploit a vulnerability to breach your systems or steal data?
Have you made recent infrastructure changes that could introduce new risks?
Do you need to maintain compliance with industry standards or legal frameworks?
Would independent testing help strengthen client and stakeholder trust?
Are you looking for a security partner that thinks like an attacker, but works for you?
If you answered yes to any of these, a tailored penetration test from CodeShield is your next step toward real confidence, and real security.
Book your free cyber security assessment consultation. Speak to our pen testing UK experts today.

Trusted by organisations across the UK





“We have used a couple of companies for pen tests in the past, but never had such an outstanding experience. The team really got to grips with our application and took a much more targeted and methodical approach to the testing. Couldn’t be happier with the service received.”
Chris Clarkson - Technical Director
“The team listened to what we wanted, added their own expertise and recommendations and then performed a bespoke test with meaningful, well set out results. The follow-up meeting between our dev team and the tester was well run and respectful. I highly recommend CodeShield and will be engaging them again for our future testing.”
Daren Martin - Founder & CEO
“We had a great experience working with CodeShield. Their team was professional and responsive, and the process was clear, fair, and well-communicated throughout. They also took the time to adjust their solution to better suit our needs. We’re pleased with our decision to work with them and would recommend their services.”
Hanan Amar - CTO
“We had a great experience using CodeShield for our Penetration Test. Tom and Dan ensured the whole process ran smoothly and we were very pleased with the quality of the testing and the report. Post-test support was also excellent.”
Brian Eyre - Engineering Delivery Manager
“Tom, Daniel, Euan and the team were very professional and explained in simple terms where we needed to make improvements. Would highly recommend.”
Paul Esson - Marketing Consultant
“Tom and team helped greatfully to arrange our pentest to suit our scope and requirements. We will be working with them again in the near future for further tests. Well done guys.”
Adrian Morris - Director
Built on standards, backed by certifications
As a trusted penetration testing company, we maintain strict quality standards across all our penetration testing services. Every CodeShield engagement is led by certified professionals who bring deep technical expertise to every cyber security assessment.



A closer look at our penetration testing process
1. Scoping
We collaborate with you to define the scope, objectives, and boundaries of the penetration test. This includes identifying the systems, applications, or networks to be tested, along with any exclusions or limitations. Key objectives such as identifying vulnerabilities, testing compliance requirements, or assessing security posture are established. Clear rules of engagement ensure alignment with your goals while minimising the risk of operational disruption.
2. Intel Gathering
We conduct reconnaissance to collect information about the target environment. This includes identifying exposed services, IP addresses, domains, and any publicly accessible information that could be leveraged by attackers. The data collected during this phase forms the foundation for identifying potential vulnerabilities and attack vectors in subsequent stages.
3. Vulnerability Analysis
Our team systematically evaluates the target systems for vulnerabilities. This includes identifying misconfigurations, unpatched software, weak authentication mechanisms, or insecure communication channels. The analysis may involve automated scanning tools as well as manual testing to ensure thoroughness and accuracy. Vulnerabilities are prioritised based on their potential impact and exploitability.
4. Exploitation
In this phase, we attempt to exploit identified vulnerabilities to determine their real-world impact. This may involve gaining unauthorised access, escalating privileges, or accessing sensitive data. Exploitation activities are conducted in a controlled manner to ensure system stability and data integrity, demonstrating how an attacker could leverage weaknesses to compromise the target environment.
If exploitation is successful, we assess the potential for further compromise, such as pivoting within the network, maintaining persistence, or accessing additional resources. This phase mimics real-world attacker behavior to understand the full scope of impact and identify additional security gaps.
5. Reporting
We provide a comprehensive report detailing the vulnerabilities discovered, the methods used to exploit them, and their potential impact on your organisation. Each finding is accompanied by practical recommendations for remediation, prioritised by severity and risk. The report is designed to be actionable for technical teams while being accessible to non-technical stakeholders.
6. Debriefing
The engagement concludes with a debriefing session to review the results and discuss their implications. We provide an overview of the vulnerabilities, demonstrate potential exploitation scenarios, and answer any questions. This session ensures a clear understanding of the findings and offers actionable guidance for strengthening your security posture.
Frequently asked questions (FAQs)
What is a pen test?
A pen test, short for penetration testing, is part of a broader cyber security assessment where ethical hackers simulate cyber-attacks on your systems, networks, or applications. The goal of this security penetration testing is to identify vulnerabilities before malicious attackers can exploit them.
Following any test, you’ll receive a clear report outlining the risks, along with actionable remediation steps.
How long is a pen test?
The length of a penetration testing service depends on the scope, size, and complexity of your environment. Whether it’s a simple web app or an enterprise network, our pen testing UK experts work with you beforehand to define a timeline and ensure minimal disruption.
What's the difference between penetration testing and vulnerability scanning?
Vulnerability scanning is typically automated and identifies known issues. Penetration testing, on the other hand, involves human experts attempting to exploit those vulnerabilities to understand the true risk and business impact. That’s why engaging with a skilled penetration testing company adds significant value, beyond what tools alone can offer.
What are the different types of pen tests?
There are multiple penetration testing services available, including:
White Box Testing – The tester has full knowledge of the system.
Black Box Testing – The tester has no prior access or information.
Grey Box Testing – A blend of the two, offering partial knowledge for realistic simulations.
A comprehensive cyber security assessment often includes a mix of these approaches to provide complete coverage.
Will my business be disrupted during testing?
Our penetration testing services are designed to minimise disruption. When possible, testing is performed on a staging or non-production environment. If testing in production is necessary, we’ll outline all precautions during the security penetration testing scoping phase.
How long does it take for a pen test to run out?
Industry best practice recommends conducting penetration testing at least once per year or after any major infrastructure change. If your business operates under frameworks like PCI DSS or ISO 27001, annual testing is typically required. Our pen testing UK team can help you define the right cadence as part of your broader cyber security assessment strategy. requires annual testing to maintain.
Ready for pen testing that supports you at every step?
Get a free penetration test quote today:
Excellent rating
Based on 10 reviewsTrustindex verifies that the original source of the review is Google. Friendly and professional penestration testing for our web appTrustindex verifies that the original source of the review is Google. We recently engaged Code Shield to carry out penetration testing for one of our clients, and the service was nothing short of excellent. Both Tom and Dan were extremely knowledgeable and professional throughout the process. Their clear communication and technical expertise made the entire experience smooth and efficient. We look forward to working with them again when the need arises and would highly recommend their services.Trustindex verifies that the original source of the review is Google. We had a great experience working with CodeShield. Their team was professional and responsive, and the process was clear, fair, and well-communicated throughout. They also took the time to adjust their solution to better suit our needs. We’re pleased with our decision to work with them and would recommend their services.Trustindex verifies that the original source of the review is Google. We've used a number of CREST assured pen testing companies over the last 10 years, however CodeShield have been the first to exceed my expectations. The team listened to what we wanted, added their own expertise and recommendations and then performed a bespoke test with meaningful, well set out results. The follow-up meetings between our dev team and the testers was well run and respectful. I highly recommend CodeShield and will be engaging them again for our future testing.Trustindex verifies that the original source of the review is Google. We had a great experience using CodeShield for our Penetration Test. Tom and Dan ensured the whole process ran smoothly and we were very pleased with the quality of the testing and the report. Post-test support was also excellent.Trustindex verifies that the original source of the review is Google. Tom, Daniel, Euan and the team were very professional and explained in simple terms where we needed to make improvements. Would highly recommend.Trustindex verifies that the original source of the review is Google. Tom and team helped greatfully to arrange our pentest to suit our scope and requirements. We will be working with them again in the near future for further tests. Well done guys.Trustindex verifies that the original source of the review is Google. We have used a couple of companies for pen tests in the past, but never had such an outstanding experience. The team really got to grips with our application and took a much more targeted and methodical approach to the testing. Couldn't be happier with the service received.