Web Application
Penetration Testing
Find hidden risks before attackers do. Get expert-led, OWASP penetration testing with clear, actionable results. No false positives, no fluff.
Build user trust, meet OWASP Penetration Testing and Web App Security Audit compliance, and strengthen your defences with support from experienced specialists.




Get a fast web app pen test quote:
Experts in web application penetration testing
App & API
Coverage
We deliver comprehensive web app security assessments across traditional platforms and modern APIs, ensuring no critical risks or vulnerabilities are overlooked.
OWASP
Testing
Using the industry-standard OWASP penetration testing methodology, we evaluate your applications against recognised security threats and real-world attack scenarios.
Professional
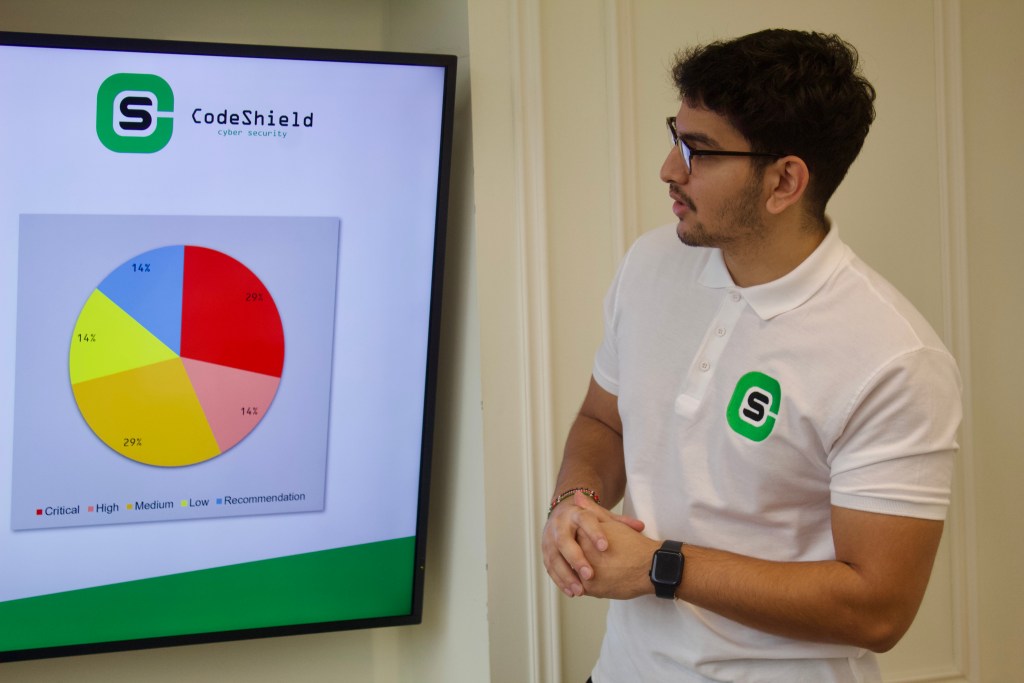
Reporting
Our reporting goes beyond raw data providing clear, actionable insight into your OWASP Penetration Testing and Web App Security Audit results for quicker remediation.
Continuous
Support
As a trusted OWASP Penetration Testing and Web App Security Audit provider, we offer ongoing expert support to help you maintain a strong and adaptable security posture.
What is web application penetration testing?
Web application penetration testing is a targeted web app security assessment where our experts simulate real-world attacks against your web applications and APIs, helping you find and fix vulnerabilities before attackers do. Unlike automated scans or surface-level reviews, our testing is hands-on, thorough, and aligned with OWASP Penetration Testing and Web App Security Audit compliance standards.
At CodeShield, we dig deep into your application’s code, architecture, configurations, and exposed interfaces. Using proven techniques and the OWASP Top Ten as a foundation, we uncover critical risks and explain them in plain English, so your team can remediate with clarity and confidence.

What you get with CodeShield’s web application pen testing:
In-depth OWASP penetration testing, targeting the most dangerous and common vulnerabilities
Testing from both authenticated and unauthenticated user perspectives
Full API testing. Every connected endpoint gets equal scrutiny
A complete, prioritised report tailored for your team. Jargon-free, with actionable remediation steps
Ongoing support from our OWASP Penetration Testing and Web App Security Audit testing company. We help you fix issues, not just find them
Trusted by organisations across the UK





“We have used a couple of companies for pen tests in the past, but never had such an outstanding experience. The team really got to grips with our application and took a much more targeted and methodical approach to the testing. Couldn’t be happier with the service received.”
Chris Clarkson - Technical Director
“The team listened to what we wanted, added their own expertise and recommendations and then performed a bespoke test with meaningful, well set out results. The follow-up meeting between our dev team and the tester was well run and respectful. I highly recommend CodeShield and will be engaging them again for our future testing.”
Daren Martin - Founder & CEO
“We had a great experience working with CodeShield. Their team was professional and responsive, and the process was clear, fair, and well-communicated throughout. They also took the time to adjust their solution to better suit our needs. We’re pleased with our decision to work with them and would recommend their services.”
Hanan Amar - CTO
“We had a great experience using CodeShield for our Penetration Test. Tom and Dan ensured the whole process ran smoothly and we were very pleased with the quality of the testing and the report. Post-test support was also excellent.”
Brian Eyre - Engineering Delivery Manager
“Tom, Daniel, Euan and the team were very professional and explained in simple terms where we needed to make improvements. Would highly recommend.”
Paul Esson - Marketing Consultant
“Tom and team helped greatfully to arrange our pentest to suit our scope and requirements. We will be working with them again in the near future for further tests. Well done guys.”
Adrian Morris - Director
Common web application vulnerabilities
Web applications vary widely, from basic brochure sites to complex SaaS platforms and API-driven systems. Regardless of the type, attackers constantly probe for weaknesses. That’s why our web application penetration testing goes far beyond basic scans.
At CodeShield, every web app pen testing engagement includes deep, manual analysis aligned with the OWASP penetration testing framework, covering the OWASP Top Ten and real-world threats often missed by automated tools.
Our OWASP Penetration Testing and Web App Security Audit assessments target vulnerabilities such as:
- Improper Access Controls
- Stored Cross-Site Scripting
- Outdated Website Libraries/Components
- Cross-Site Request Forgery
- SQL Injection
- Reflected Cross-Site Scripting
- CSV Injection
- Arbitrary File Upload
- Server-Side Request Forgery
- Unrestricted File Upload
- Outdated Website Libraries/Components
Benefits of web application penetration testing
Wondering if web application penetration testing is worth the investment? Here’s how your business can benefit:
See your app from an attacker’s perspective with a real-world web app security assessment.
Identify critical vulnerabilities and likely attack paths, not just generic issues from automated tools.
Receive clear, actionable remediation guidance, not just technical jargon.
Strengthen trust with clients, partners, and stakeholders by proving your OWASP Penetration Testing and Web App Security Audit compliance is independently verified.
- Meet compliance requirements with ISO 27001, GDPR, PCI DSS, with expert-led OWASP Penetration Testing and Web App Security Audit testing.
Is web application penetration testing right for you?
If you manage a website, web platform, or API, ask yourself:
Could an attacker exploit your application to access sensitive data or internal systems?
Is there a risk of compromised user accounts or stolen credentials?
Are your APIs protected against modern, real-world threats?
Does your app handle personally identifiable information (PII)?
Would your clients value third-party validation of your OWASP Penetration Testing and Web App Security Audit compliance?
If you answered yes to any of these, a tailored OWASP Penetration Testing and Web App Security Audit assessment from CodeShield is your next step toward real confidence, and real security.
Get in touch today for a free consultation from our web app pen testing experts and a no-obligation quote tailored to your application.

A closer look at our web application pen testing process
1. Scoping
Our team collaborates with you to define a precise approach for testing your web application. This phase establishes the scope by identifying key areas such as application functionalities, APIs, user roles, and integrations to be tested. Clear objectives, timelines, and deliverables are agreed upon, ensuring alignment with your business priorities. Our experienced testers provide insights during scoping to ensure a seamless transition into testing while maintaining continuity throughout the engagement.
2. Intel Gathering
We perform reconnaissance specifically focused on your web application. This includes analysing the application’s public-facing components, such as login mechanisms, input fields, APIs, frameworks, and third-party integrations. Using advanced tools and techniques, we gather critical data like technology stacks, exposed endpoints, and potential entry points. This information helps to map the application’s attack surface and prepares the tester to maximise the effectiveness of the following testing phases.
3. Vulnerability Analysis
In this phase, we systematically assess your web application for security weaknesses. This includes testing for common vulnerabilities such as SQL injection, cross-site scripting (XSS), broken authentication, insecure direct object references (IDOR), and misconfigured security headers. Our analysis evaluates these issues in the context of your application’s architecture, prioritising vulnerabilities that pose the most significant risk to user data, system integrity, or business operations.
4. Exploitation
We then simulate real-world attack scenarios by actively exploiting identified vulnerabilities. For example, we might bypass authentication mechanisms, extract sensitive data, or manipulate session tokens. This phase focuses on demonstrating the potential impact of exploited flaws, such as unauthorised access to user accounts or the compromise of sensitive business data. Every action is controlled, ensuring the integrity of your application remains intact throughout the process.
5. Reporting
Once testing is complete, we compile a comprehensive report that is tailored to web application security. This document includes detailed findings for vulnerabilities, technical proof-of-concept (PoC) evidence, exploitation outcomes, and a risk assessment matrix. For each issue, we provide actionable remediation guidance that aligns with best practices and industry standards. The report is structured to support both technical teams and decision-makers, ensuring clarity and prioritisation.
6. Debriefing
This phase is a collaborative session where we present the findings specific to your web application and discuss their implications. We walk you through the vulnerabilities, demonstrate exploitation outcomes where necessary, and answer any questions about the risks. Additionally, we provide strategic guidance for mitigation and ongoing improvements tailored to the unique features and challenges of your web application.
Frequently asked questions (FAQs)
What is the primary focus of a web app pen test?
The primary goal of web app pen testing is to identify and report on security risks within your application before attackers can exploit them. Our experts simulate real-world attack scenarios to uncover vulnerabilities in your application’s configuration, logic, and code.
A comprehensive OWASP Penetration Testing and Web App Security Audit assessment should also test from multiple user roles (both authenticated and unauthenticated) to ensure full coverage of the app’s functionality and attack surface.
What can be the potential vulnerabilities in a web application?
Every web application penetration testing engagement should include, at a minimum, checks against the Open Web Application Security Project (OWASP) Top 10 vulnerabilities. In addition, our testers utilise a blend of automated tools and manual techniques to uncover as many security risks as possible. For example, this may include issues such as broken authentication, various injection techniques, and much more.
How long does it take to security test a web application?
The duration of a web application security assessment depends on:
Size – Larger applications with more functionality require more time
Complexity – Multiple user roles, authentication flows, and APIs add testing depth
Goals – Specific objectives, such as regulatory testing or deep logic reviews, affect scope
Before any engagement, we run a detailed scoping process to tailor the web app pen testing to your specific needs.
What information is required when scoping a web app pen test?
Accurate scoping starts with a brief walk through or demo of the application. This helps our testers understand the app’s structure, user journeys, and complexity.
We’ll discuss:
Number of pages and functional areas
API exposure and third-party integrations
Authentication and role-based access
Any specific compliance or business goals
This ensures your OWASP Penetration Testing and Web App Security Audit is precise, relevant, and aligned with risk.
When is the best time to test a web application?
Ideally, test before the application goes live. After launch, schedule regular web application security assessments at least once per year, or after any major updates or new features. This approach ensures you maintain a secure posture and meet ongoing web application security compliance requirements.
Ready for pen testing that supports you at every step?
Get a free penetration test quote today:
Excellent rating
Based on 10 reviewsTrustindex verifies that the original source of the review is Google. Friendly and professional penestration testing for our web appTrustindex verifies that the original source of the review is Google. We recently engaged Code Shield to carry out penetration testing for one of our clients, and the service was nothing short of excellent. Both Tom and Dan were extremely knowledgeable and professional throughout the process. Their clear communication and technical expertise made the entire experience smooth and efficient. We look forward to working with them again when the need arises and would highly recommend their services.Trustindex verifies that the original source of the review is Google. We had a great experience working with CodeShield. Their team was professional and responsive, and the process was clear, fair, and well-communicated throughout. They also took the time to adjust their solution to better suit our needs. We’re pleased with our decision to work with them and would recommend their services.Trustindex verifies that the original source of the review is Google. We've used a number of CREST assured pen testing companies over the last 10 years, however CodeShield have been the first to exceed my expectations. The team listened to what we wanted, added their own expertise and recommendations and then performed a bespoke test with meaningful, well set out results. The follow-up meetings between our dev team and the testers was well run and respectful. I highly recommend CodeShield and will be engaging them again for our future testing.Trustindex verifies that the original source of the review is Google. We had a great experience using CodeShield for our Penetration Test. Tom and Dan ensured the whole process ran smoothly and we were very pleased with the quality of the testing and the report. Post-test support was also excellent.Trustindex verifies that the original source of the review is Google. Tom, Daniel, Euan and the team were very professional and explained in simple terms where we needed to make improvements. Would highly recommend.Trustindex verifies that the original source of the review is Google. Tom and team helped greatfully to arrange our pentest to suit our scope and requirements. We will be working with them again in the near future for further tests. Well done guys.Trustindex verifies that the original source of the review is Google. We have used a couple of companies for pen tests in the past, but never had such an outstanding experience. The team really got to grips with our application and took a much more targeted and methodical approach to the testing. Couldn't be happier with the service received.





