Blog posted on 7th February 2026
ISO 27001 Compliance: The Role of Penetration Testing

Introduction:
Organisations today face constant pressure to protect sensitive data while meeting regulatory and compliance requirements. Cyber threats continue to evolve, and businesses must demonstrate that their security controls are not only implemented but also effective.
One of the most widely recognised standards for managing information security is ISO 27001. This framework helps organisations establish structured processes for protecting information assets and managing cyber security risks.
However, achieving ISO 27001 compliance is not simply about policies and documentation. Organisations must also validate that their security controls work in real-world conditions. This is where expert-led penetration testing plays an important role.
By combining ISO 27001 security frameworks with controlled penetration testing, organisations gain clear insight into real vulnerabilities and potential attack paths before malicious actors exploit them.
What Is ISO 27001
ISO 27001 is an internationally recognised information security standard developed by the International Organisation for Standardisation (ISO) and the International Electrotechnical Commission (IEC).
The standard provides organisations with a framework for establishing and maintaining an Information Security Management System (ISMS). This system helps businesses identify risks, implement security controls, and continuously improve their information security practices.
For organisations operating digital systems or handling sensitive data, ISO 27001 compliance demonstrates a strong commitment to protecting information and managing cyber risk responsibly.
Information Security Management Systems
An Information Security Management System (ISMS) forms the foundation of ISO 27001 compliance.
An ISMS provides a structured framework for managing information security across an organisation’s systems, processes and data environments. It focuses on three core principles:
Confidentiality
Ensuring sensitive information is accessible only to authorised individuals.
Integrity
Protecting data from unauthorised modification or corruption.
Availability
Ensuring systems and information remain accessible when required.
Through risk assessments, technical controls and security policies, an ISMS helps organisations protect business-critical information while maintaining regulatory compliance.
However, organisations must also ensure these controls work effectively when exposed to real attack techniques. This is where penetration testing provides valuable validation.
Why Organisations Pursue ISO 27001 Certification
Many organisations pursue ISO 27001 certification to strengthen trust with clients, regulators and stakeholders.
Certification demonstrates that a business follows recognised information security practices and actively manages cyber risk. This can be particularly important for organisations handling sensitive customer data or operating in regulated sectors.
ISO 27001 compliance also supports business growth. Many clients and partners now expect security assurance before working with suppliers, making certification a competitive advantage.
The framework also encourages continuous improvement, ensuring organisations regularly review and strengthen their cyber security practices.
What Is Penetration Testing
Penetration testing is a controlled cyber security assessment designed to uncover vulnerabilities before attackers do.
Often referred to as ethical hacking, penetration testing involves experienced security professionals attempting to exploit weaknesses in systems, applications or networks in a controlled environment.
Unlike automated vulnerability scans, penetration testing is a manual, expert-led process. Skilled testers analyse systems, simulate attacker behaviour and explore potential attack paths to identify real security risks.
At CodeShield, penetration testing is never a generic checklist exercise. Each engagement is carefully scoped and tailored to the organisation’s environment, ensuring testing focuses on real risks rather than theoretical issues.
Identifying Security Vulnerabilities
One of the key objectives of penetration testing is identifying security weaknesses that could allow attackers to gain access to systems or sensitive information.
These vulnerabilities may include:
- Misconfigured systems or servers
- Weak authentication mechanisms
- Outdated software or insecure services
- Application security flaws
- Network segmentation weaknesses
Expert testers analyse these issues and determine whether they can be exploited to compromise systems or access sensitive data.
By identifying vulnerabilities early, organisations gain the opportunity to strengthen their security posture before attackers discover these weaknesses.
Simulating Real World Attacks
Penetration testing goes beyond automated scanning tools by replicating the techniques used by real attackers.
Security professionals simulate realistic attack scenarios to understand how vulnerabilities could be chained together to compromise systems.
This may involve attempts to:
- Exploit application vulnerabilities
- Escalate privileges within systems
- Access sensitive data or internal resources
- Move laterally across networks
These practical simulations help organisations understand how attackers might breach their defences and reveal weaknesses that automated tools often miss.
How Penetration Testing Supports ISO 27001 Compliance
ISO 27001 requires organisations to identify and manage information security risks. While the standard outlines how to implement security controls, organisations must also demonstrate that these controls function effectively.
Penetration testing provides independent validation of those controls.
By uncovering exploitable vulnerabilities and demonstrating potential attack paths, penetration testing supports the risk management objectives of ISO 27001 and helps organisations strengthen their cyber security strategy.
Strengthening Security Controls
Security controls within an ISMS are designed to protect systems, networks and data from unauthorised access.
However, controls that appear secure in theory may still contain weaknesses when tested under realistic attack conditions.
Penetration testing evaluates how these controls perform against simulated attacks. Testing may reveal gaps in authentication processes, network configuration or application security that require attention.
These insights allow organisations to improve their security posture and strengthen the effectiveness of their information security controls.
Supporting Risk Management
Risk management is central to ISO 27001 compliance.
Organisations must identify potential threats, evaluate their likelihood and impact, and implement appropriate mitigation strategies.
Penetration testing supports this process by demonstrating how vulnerabilities could be exploited in practice. This helps organisations prioritise security improvements based on real risk rather than theoretical assumptions.
The result is a more focused and effective cyber security strategy.
Continuous Security Improvement
ISO 27001 promotes a continuous improvement approach to information security.
Cyber threats evolve constantly, and organisations must regularly evaluate their defences to remain resilient.
Periodic penetration testing helps organisations identify emerging vulnerabilities, validate security controls and strengthen their defensive strategy over time.
This ongoing testing helps maintain strong security practices as systems, technologies and threats continue to evolve.
When Organisations Should Perform Penetration Testing
Penetration testing should be integrated into an organisation’s wider cyber security and risk management processes.
Testing is often conducted:
During security audits or compliance assessments
Independent testing can support internal reviews and provide evidence of active security evaluation.
After infrastructure or system changes
Major upgrades, software deployments or architectural changes may introduce new vulnerabilities that require testing.
On a regular testing schedule
Many organisations perform penetration testing annually, while high-risk environments may require more frequent assessments.
Types of Penetration Testing
Different types of penetration testing may be required depending on an organisation’s infrastructure and risk profile.
Network Penetration Testing
Network testing identifies vulnerabilities within internal or external network environments, including firewalls, servers and communication protocols.
Web Application Penetration Testing
Web applications are a common target for attackers. Testing focuses on identifying vulnerabilities such as authentication flaws, injection attacks and insecure data handling.
Infrastructure Security Testing
Infrastructure testing evaluates the security of servers, system configurations, databases and supporting technologies.
Each test provides valuable insight into potential attack paths within an organisation’s environment.
Benefits of Penetration Testing for ISO 27001
Penetration testing offers several strategic advantages for organisations working toward ISO 27001 compliance.
Identifying Hidden Security Risks
Complex IT environments often contain vulnerabilities that remain undetected during routine monitoring. Penetration testing uncovers these weaknesses before attackers can exploit them.
Supporting Compliance Requirements
Expert security testing can help organisations demonstrate due diligence to clients, regulators and auditors by proving that security controls are regularly evaluated.
Strengthening Cyber Security Strategy
Penetration testing provides organisations with clear insights into their security exposure, helping them prioritise improvements and strengthen long-term resilience.
Conclusion & Author:
ISO 27001 compliance provides organisations with a structured framework for managing information security risks. However, implementing policies and controls alone does not guarantee effective protection.
Penetration testing plays a crucial role in validating those controls and uncovering vulnerabilities that could compromise critical systems.
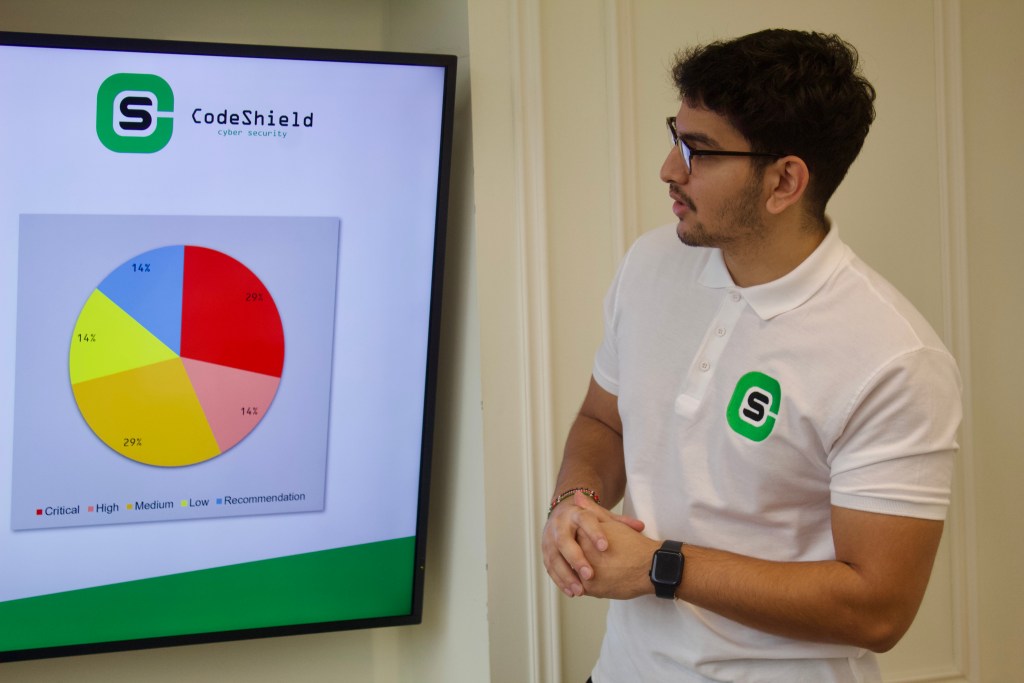
At CodeShield, our penetration testing services focus on delivering clear, credible security insights through expert-led testing. Every engagement is tailored to the organisation’s environment, ensuring testing identifies real vulnerabilities and meaningful security risks.
By combining structured security frameworks with practical testing, organisations can strengthen their defences, build stakeholder confidence and maintain resilient cyber security practices.
Have a different question?
Speak to a security expert today: