Network Penetration Testing
Proactively secure your business with expert-led network penetration testing that simulates real-world attacks, not just automated scans. Uncover and remediate vulnerabilities across your network infrastructure before they can be exploited.




Get a fast network pentesting quote:
Experienced Network and Infrastructure Penetration Testing Experts
Full Network Coverage
Our network penetration testing services cover both internal and external systems. From firewalls to workstations, we identify weaknesses across your environment, ensuring your entire network infrastructure is thoroughly assessed.
Trusted
Methodology
As a trusted network security audit company, we follow the Penetration Testing Execution Standard (PTES) to deliver consistent, high-quality results. Every network pentesting project is structured for accuracy, repeatability, and reliability.
Professional
Reporting
You’ll receive tailored, easy-to-understand reports that highlight genuine risks, not noise. Our reporting helps you prioritise fixes based on business impact, ensuring your network security testing delivers real value.
Continuous
Support
Our experts stay involved beyond the test, offering ongoing guidance as part of a complete internal pentest or external pentest strategy. Stay ahead of new threats with long-term, expert-driven support.
Understanding Network Penetration Testing and Network Vulnerability Assessment
Network penetration testing is a controlled simulation of cyber attacks targeting your organisation’s network infrastructure. The objective? To uncover and remediate vulnerabilities before real attackers can exploit them. Unlike automated scans, our network pentesting approach is manual, methodical, and tailored to your environment.
At CodeShield, we conduct both internal network penetration testing and external pentests, assessing your systems from all relevant angles. We analyse network traffic, firewall rules, system configurations, and access controls, delivering real insight.
Our methodology follows the industry-recognised PTES standard, ensuring that every network security testing engagement is comprehensive, consistent, and actionable.

What’s included in CodeShield’s network pentesting?
External pentest and internal pentest engagements guided by the PTES framework
In-depth firewall and open port reviews to assess perimeter resilience
Server and system configuration audits to reduce attack surface and prevent data leakage
Clear, prioritised reports with remediation advice, designed for both technical and business teams
Post-test access to expert guidance from a leading network security audit company
Trusted by organisations across the UK





“We have used a couple of companies for pen tests in the past, but never had such an outstanding experience. The team really got to grips with our application and took a much more targeted and methodical approach to the testing. Couldn’t be happier with the service received.”
Chris Clarkson - Technical Director
“The team listened to what we wanted, added their own expertise and recommendations and then performed a bespoke test with meaningful, well set out results. The follow-up meeting between our dev team and the tester was well run and respectful. I highly recommend CodeShield and will be engaging them again for our future testing.”
Daren Martin - Founder & CEO
“We had a great experience working with CodeShield. Their team was professional and responsive, and the process was clear, fair, and well-communicated throughout. They also took the time to adjust their solution to better suit our needs. We’re pleased with our decision to work with them and would recommend their services.”
Hanan Amar - CTO
“We had a great experience using CodeShield for our Penetration Test. Tom and Dan ensured the whole process ran smoothly and we were very pleased with the quality of the testing and the report. Post-test support was also excellent.”
Brian Eyre - Engineering Delivery Manager
“Tom, Daniel, Euan and the team were very professional and explained in simple terms where we needed to make improvements. Would highly recommend.”
Paul Esson - Marketing Consultant
“Tom and team helped greatfully to arrange our pentest to suit our scope and requirements. We will be working with them again in the near future for further tests. Well done guys.”
Adrian Morris - Director
Common Network Vulnerabilities Found During Network Security Audits
Network penetration testing applies to everything from a single exposed IP address to complex, segmented internal environments. At CodeShield, our network penetration testing services follow the PTES framework for structure and consistency, but we go beyond the basics. Our experts focus on identifying the vulnerabilities that truly matter to your business, whether through an external pentest or deep internal network penetration testing.
Our team commonly tests for:
- SSL Misconfigurations
- Missing HTTP Security Headers
- Outdated Website Libraries/Components
- SMB Signing not Required
- Excessive Information Disclosure
- Unnecessary Open Services
- Host Header Injection
- Outdated and Unsupported Third Party Software
- SSH Misconfiguration
- Click Jacking

Benefits of network penetration testing
Considering a network penetration test? Here’s how your organisation can benefit:
Gain full visibility into vulnerabilities across your network infrastructure, eliminate hidden risks before they’re exploited
Strengthen trust with clients and stakeholders through expert-led network security testing
Understand how attackers could move laterally via privilege escalation or poor configurations
Get actionable insights that show the business impact, not just technical issues
Meet compliance goals (ISO 27001, GDPR, PCI DSS) with assessments from a trusted network security audit company.
Is network penetration testing right for you?
If you’re responsible for securing your internal or external systems, ask yourself:
Are all systems patched and securely configured?
Could weak or default credentials still exist in your environment?
Have all external-facing services been thoroughly tested through an external pentest?
Could an insider or malware exploit internal weaknesses without detection?
Is there a risk of sensitive data leaking from your network?
If you’re unsure about any of these, a network pentesting engagement with CodeShield—covering both internal pentest and external testing—can give you the clarity, confidence, and control you need.
Get in touch today for a free consultation with our network pen testing experts and receive a no-obligation quote tailored to your environment.

A closer look at our network penetration testing process
1. Scoping
Our team works with you to define a comprehensive testing approach specific to your network infrastructure. This phase outlines the assets to be tested, such as internal and external network segments, devices, protocols, and systems. Key objectives, boundaries, and exclusions are identified to ensure alignment with your security and compliance requirements. Our experts ensure that all critical components of your network are considered, setting the stage for a thorough and effective engagement.
2. Intel Gathering
We initiate reconnaissance by collecting detailed information about your network. For external networks, this involves identifying public-facing IP addresses, domain names, and exposed services. For internal networks, we map the infrastructure, including devices, subnets, VLANs, and communication pathways. Utilising both passive and active techniques, we gather insights about open ports, running services, software versions, and potential misconfigurations. This step is critical for identifying the network’s attack surface.
3. Vulnerability Analysis
Our experts systematically evaluate your network for security vulnerabilities. This involves identifying common issues such as unpatched systems, misconfigured firewalls, weak credentials, outdated protocols, and insecure network architectures. We utilise industry-leading tools and manual techniques to uncover vulnerabilities while analysing their potential impact on your network’s integrity, availability, and confidentiality.
4. Exploitation
In this phase, we simulate real-world attacks to exploit identified vulnerabilities. This may include gaining unauthorised access to critical systems, elevating privileges, or intercepting sensitive data through techniques such as credential cracking, lateral movement, or man-in-the-middle (MITM) attacks. The goal is to demonstrate how an attacker could compromise your network, providing valuable insight into the potential business impact of these security gaps.
5. Reporting
We deliver a detailed report summarising the penetration test findings in the context of your network. This includes descriptions of vulnerabilities, exploitation techniques used, and the risk they pose to your infrastructure. Each issue is accompanied by clear remediation steps to help your technical team address the root cause. The report is structured to be accessible to both technical and non-technical stakeholders, with an emphasis on prioritising higher-risk findings.
6. Debriefing
The engagement concludes with a debriefing session, allowing you to discuss the results directly with the assigned tester. During this interactive meeting, we provide an overview of the vulnerabilities, exploitation outcomes, and their implications for your network. We also discuss strategic recommendations to strengthen your network’s security posture and address any questions to ensure a clear understanding of the next steps.
Network Penetration Testing FAQs and Common Queries
What is external network penetration testing?
An external pentest focuses on identifying vulnerabilities across your network perimeter, examining externally facing IPs, services, and systems that could be exploited by remote attackers. The goal is to highlight weaknesses that a hacker could use to gain initial access, and to deliver a clear, actionable report to help you strengthen your perimeter defences.
Internal and external network penetration testing
While external testing targets internet-facing infrastructure, internal network penetration testing simulates threats that originate inside the organisation—whether from malicious insiders or compromised users. This type of internal pentest explores lateral movement, privilege escalation, and misconfigurations within your environment.
A complete network pentesting strategy should often include both internal and external perspectives to provide full coverage of potential threats.
Types of network vulnerabilities
A network security testing engagement can uncover a wide range of weaknesses. Common examples include:
Weak or reused passwords
Misconfigured servers and open ports
Inadequate firewall rules or exposed services
Insecure authentication or access control methods
These findings help your team focus remediation efforts where they matter most.
What’s in a network penetration testing report?
Every network penetration testing services engagement includes a structured, plain-English report, which typically includes:
Introduction & Project Scope
Executive Summary – high-level risks and overall findings
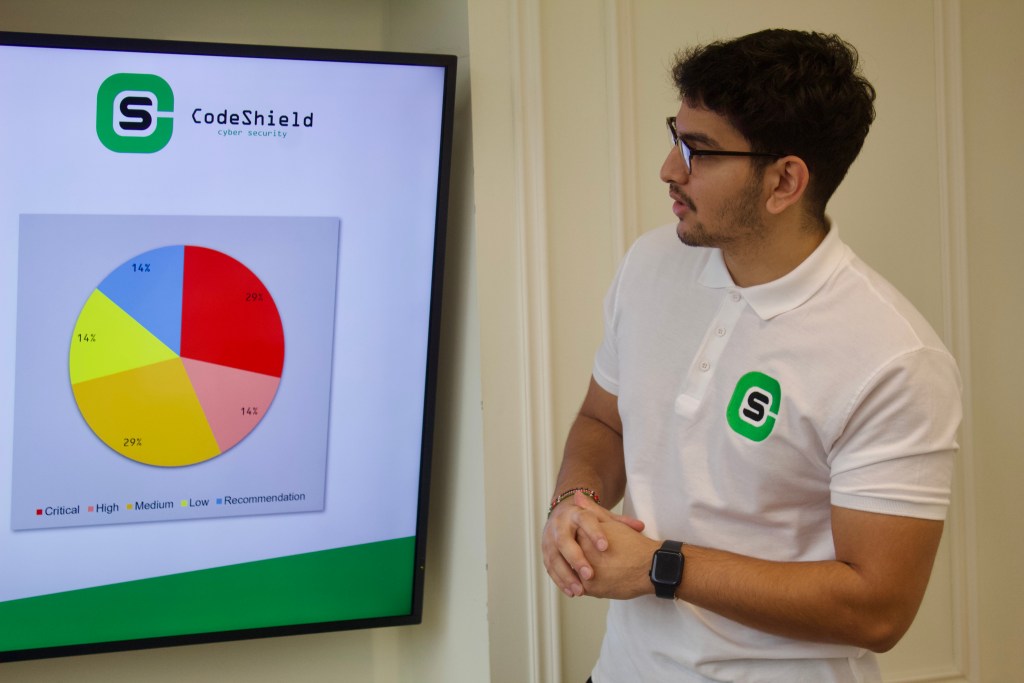
Assessment Results – detailed technical vulnerabilities and risk ratings
Appendices – supporting evidence, methodology, and remediation references
This format ensures clarity for both technical and non-technical stakeholders.
How do you scope a network test?
As a collaborative network security audit company, we always involve our penetration testers in the scoping phase to capture the right details from day one. Key areas discussed include:
Testing objectives and risk drivers
Assets and environments in scope
Budget, timeframes, and logistical constraints
This results in a tailored network penetration testing project that aligns precisely with your business goals and risk appetite.
Ready for pen testing that supports you at every step?
Get a free penetration test quote today:
Excellent rating
Based on 10 reviewsTrustindex verifies that the original source of the review is Google. Friendly and professional penestration testing for our web appTrustindex verifies that the original source of the review is Google. We recently engaged Code Shield to carry out penetration testing for one of our clients, and the service was nothing short of excellent. Both Tom and Dan were extremely knowledgeable and professional throughout the process. Their clear communication and technical expertise made the entire experience smooth and efficient. We look forward to working with them again when the need arises and would highly recommend their services.Trustindex verifies that the original source of the review is Google. We had a great experience working with CodeShield. Their team was professional and responsive, and the process was clear, fair, and well-communicated throughout. They also took the time to adjust their solution to better suit our needs. We’re pleased with our decision to work with them and would recommend their services.Trustindex verifies that the original source of the review is Google. We've used a number of CREST assured pen testing companies over the last 10 years, however CodeShield have been the first to exceed my expectations. The team listened to what we wanted, added their own expertise and recommendations and then performed a bespoke test with meaningful, well set out results. The follow-up meetings between our dev team and the testers was well run and respectful. I highly recommend CodeShield and will be engaging them again for our future testing.Trustindex verifies that the original source of the review is Google. We had a great experience using CodeShield for our Penetration Test. Tom and Dan ensured the whole process ran smoothly and we were very pleased with the quality of the testing and the report. Post-test support was also excellent.Trustindex verifies that the original source of the review is Google. Tom, Daniel, Euan and the team were very professional and explained in simple terms where we needed to make improvements. Would highly recommend.Trustindex verifies that the original source of the review is Google. Tom and team helped greatfully to arrange our pentest to suit our scope and requirements. We will be working with them again in the near future for further tests. Well done guys.Trustindex verifies that the original source of the review is Google. We have used a couple of companies for pen tests in the past, but never had such an outstanding experience. The team really got to grips with our application and took a much more targeted and methodical approach to the testing. Couldn't be happier with the service received.