Penetration Testing: Find Vulnerabilities Before Cybercriminals Do
Blog posted on 20th March 2026

Introduction
Penetration testing is a controlled cyber security assessment used to identify weaknesses in systems, networks, and applications before malicious attackers can exploit them. Rather than waiting for a security incident to expose vulnerabilities, organisations can proactively evaluate their defences and understand where real risks may exist.
A penetration test simulates the techniques used by real attackers. Security specialists attempt to access systems, bypass security controls, and identify entry points that could allow unauthorised access. The objective is not disruption, but insight. By replicating realistic attack scenarios in a safe and authorised environment, organisations gain a clearer understanding of how secure their infrastructure actually is.
Unlike automated vulnerability scans, professional penetration testing relies heavily on human expertise. Skilled security professionals analyse how vulnerabilities interact with real environments and determine whether those weaknesses could realistically lead to compromise. This approach provides deeper and more accurate insights into an organisation’s cyber security posture.
For many organisations, penetration testing becomes the foundation of a stronger cyber security strategy. Identifying weaknesses early allows businesses to prioritise risk, strengthen defences, and protect sensitive systems before attackers have the opportunity to exploit them.
The Benefits of Penetration Testing
Penetration testing provides organisations with valuable insight into their security environment. By identifying vulnerabilities before attackers discover them, businesses can take proactive steps to protect their systems, data, and digital infrastructure.
Identifying vulnerabilities
One of the primary benefits of penetration testing is uncovering hidden security weaknesses. Vulnerabilities can exist across network infrastructure, applications, configuration settings, and access controls.
Without expert testing, these weaknesses may remain undetected until exploited by an attacker. A professional penetration test highlights these gaps and provides clear evidence of potential security risks.
Preventing data breaches
Data breaches can result in financial losses, regulatory penalties, and long-term reputational damage. Penetration testing helps organisations reduce this risk by identifying security flaws that could allow attackers to access confidential information.
When vulnerabilities are discovered early, organisations can take informed action to strengthen controls and protect sensitive systems.
Supporting regulatory compliance
Many cyber security frameworks and industry regulations require organisations to perform regular security assessments. Penetration testing supports compliance with standards such as:
- ISO 27001
- PCI DSS
- SOC 2
- GDPR security requirements
Independent testing demonstrates that organisations are actively managing cyber security risks and maintaining responsible governance.
Strengthening security posture
Security posture refers to the overall effectiveness of an organisation’s cyber defences. Penetration testing provides a realistic picture of where protections are strong and where improvements are needed.
With clear reporting and expert analysis, organisations can prioritise risks and focus their security investments where they matter most.
Evaluating security monitoring and response
Penetration testing can also reveal how security monitoring tools and incident response procedures perform during simulated attacks. These insights help organisations understand whether threats would be detected quickly and how effectively teams would respond.
The result is stronger preparedness for real world cyber incidents.
Types of Penetration Testing
Different systems require different testing approaches. Penetration testing can be applied across networks, applications, cloud platforms, and even human interactions within organisations.
Network Penetration Testing
Network penetration testing focuses on evaluating internal and external infrastructure. Security specialists assess servers, firewalls, routers, and connected devices to identify weaknesses that could allow attackers to gain access.
Testing often identifies misconfigurations, exposed services, and weaknesses in access controls.
Web Application Penetration Testing
Modern businesses rely heavily on web applications to deliver services and manage data. Web application penetration testing evaluates websites, platforms, and online systems to identify vulnerabilities that attackers could exploit.
Security professionals analyse authentication mechanisms, data handling processes, and input validation controls to determine whether applications are properly secured.
Mobile Application Penetration Testing
Mobile applications often store or transmit sensitive information. Mobile penetration testing evaluates how mobile software behaves on smartphones and tablets.
Testing examines application behaviour, local data storage, and communication protocols to identify weaknesses that could expose sensitive data.
Social Engineering Testing
Cyber security is not only about technology. Human behaviour can also create vulnerabilities. Social engineering testing evaluates how employees respond to manipulation attempts such as phishing emails or deceptive communications.
These exercises help organisations improve security awareness and strengthen their overall security culture.
Wireless Penetration Testing
Wireless networks can introduce security risks if not properly configured. Wireless penetration testing analyses the security of wireless access points and network encryption mechanisms.
This type of testing helps identify weaknesses that could allow attackers to access internal networks.
Physical Penetration Testing
Physical security can also influence cyber security risk. Physical penetration testing evaluates access controls, building security, and hardware protection measures.
Weak physical security can sometimes allow attackers to gain direct access to systems or sensitive equipment.
Penetration Testing Methodologies
Penetration testing can be conducted using different methodologies depending on the level of information provided to the testing team.
Black Box Testing
Black box testing simulates an external attacker with no prior knowledge of the target environment. Testers must identify vulnerabilities using publicly available information and external reconnaissance techniques.
This approach provides realistic insight into how external threats might attempt to infiltrate systems.
White Box Testing
White box testing provides testers with full knowledge of system architecture, internal networks, and software components. This enables deeper analysis and allows testers to identify complex vulnerabilities that may not be visible externally.
This methodology is often used to evaluate internal infrastructure and sensitive systems.
Grey Box Testing
Grey box testing combines elements of both black box and white box testing. Testers receive limited information about the environment, allowing them to focus on critical systems while still simulating realistic attack scenarios.
This balanced approach provides both efficiency and depth.
The Penetration Testing Process
Professional penetration testing follows a structured process designed to systematically identify and analyse security risks.
Scoping
Every engagement begins with clearly defining the scope of testing. Security specialists collaborate with the organisation to identify the systems, networks, or applications to be assessed.
Clear objectives and rules of engagement ensure testing is aligned with business requirements and avoids operational disruption.
Reconnaissance and discovery
Security professionals gather information about the target environment, including network architecture and potential entry points. This research helps testers understand the attack surface.
Vulnerability analysis and exploitation
Once potential weaknesses are identified, testers evaluate whether those vulnerabilities could realistically be exploited. This stage demonstrates the potential impact of security weaknesses.
Post exploitation analysis
If access is achieved, testers assess how far an attacker could move within the environment. This may involve identifying access to sensitive systems or lateral movement opportunities.
Reporting and debriefing
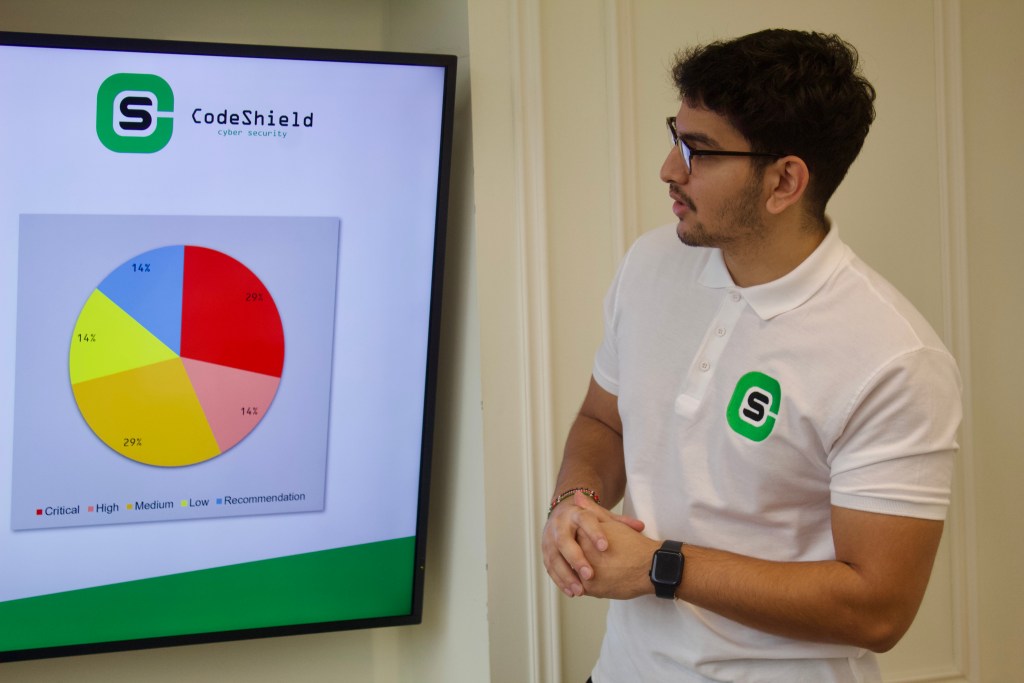
The final stage involves delivering a clear and structured report outlining discovered vulnerabilities, risk levels, and recommended remediation actions.
CodeShield focuses on providing practical, understandable reports that highlight genuine risks rather than overwhelming organisations with unnecessary technical detail. Clients receive expert debriefing and remediation guidance so they can make informed security decisions.
Why Penetration Testing Is Essential
Cyber threats continue to grow as organisations expand their digital infrastructure. Penetration testing plays a critical role in identifying weaknesses before attackers exploit them.
Increasing cyber attacks
Cyber attacks are becoming more frequent and more sophisticated. Threat actors continuously search for vulnerabilities in systems, networks, and applications.
Regular penetration testing helps organisations stay ahead of evolving threats.
Expanding attack surface
Modern organisations operate across cloud services, mobile platforms, remote networks, and web applications. Every connected system increases the potential attack surface.
Penetration testing helps identify risks across these complex environments.
Remote working security risks
Remote work environments introduce additional security challenges. Remote access systems, authentication controls, and endpoint security must all be evaluated carefully.
Penetration testing helps organisations understand whether these access points introduce new vulnerabilities.
Protecting sensitive data
Businesses handle valuable information including financial records, customer data, and intellectual property. Protecting this information is essential for maintaining trust and regulatory compliance.
Penetration testing helps ensure systems responsible for storing and processing sensitive data remain secure.
Conclusion & Author:
Penetration testing is one of the most effective ways for organisations to understand their real cyber security risks. By simulating realistic attack scenarios, businesses gain visibility into vulnerabilities that could otherwise remain hidden.
Regular testing allows organisations to strengthen their security posture, demonstrate compliance with recognised standards, and protect sensitive systems from evolving cyber threats.
CodeShield delivers expert-led penetration testing tailored to each organisation’s environment. Every engagement is performed by certified specialists who provide clear results, practical remediation guidance, and the confidence that your systems have been tested properly.
Have a different question?
Speak to a security expert today: